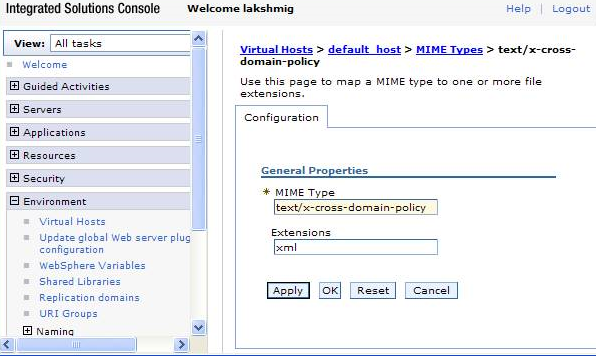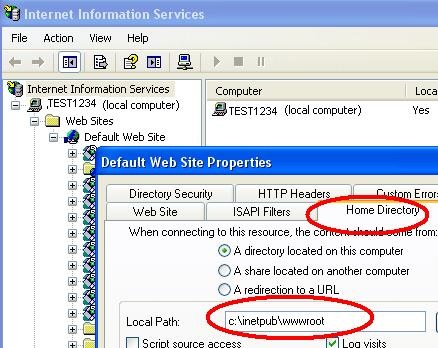
Chapter 16 Implementing Cross-Domain Single Sign-On with Cookie Hijacking Prevention (Sun OpenSSO Enterprise 8.0 Deployment Planning Guide)

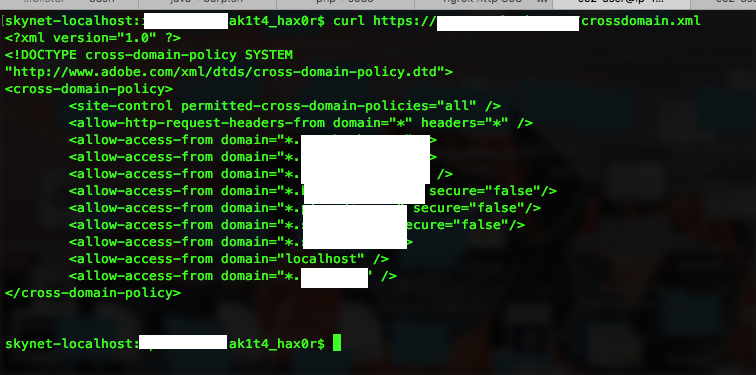
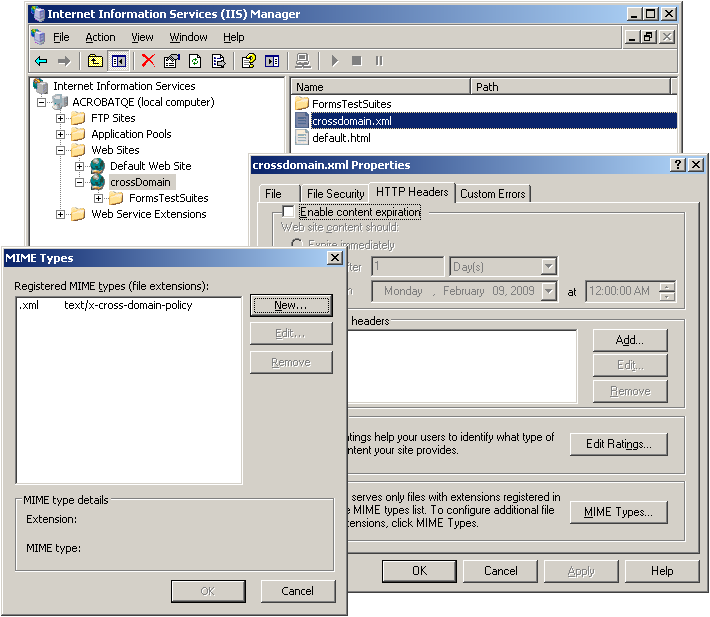
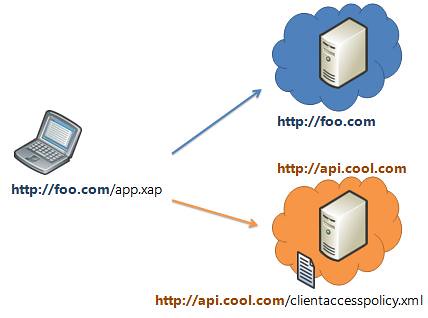
Insecure crossdomain.xml Policy file vulnerability – Learn Penetration Testing & Ethical Hacking | Julio Della Flora
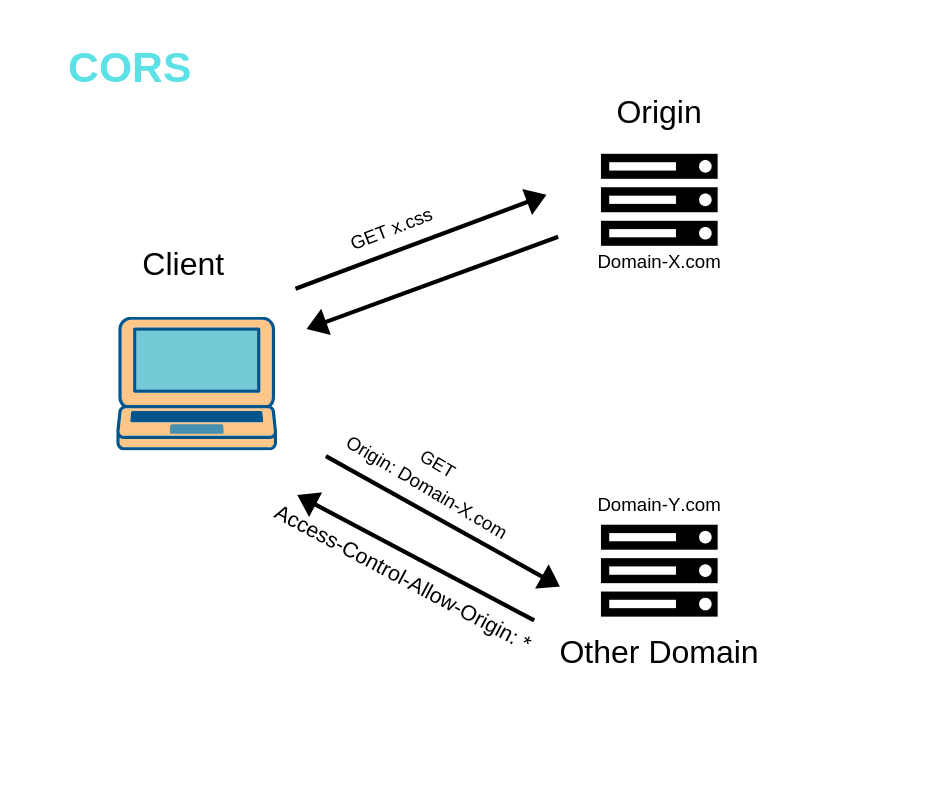
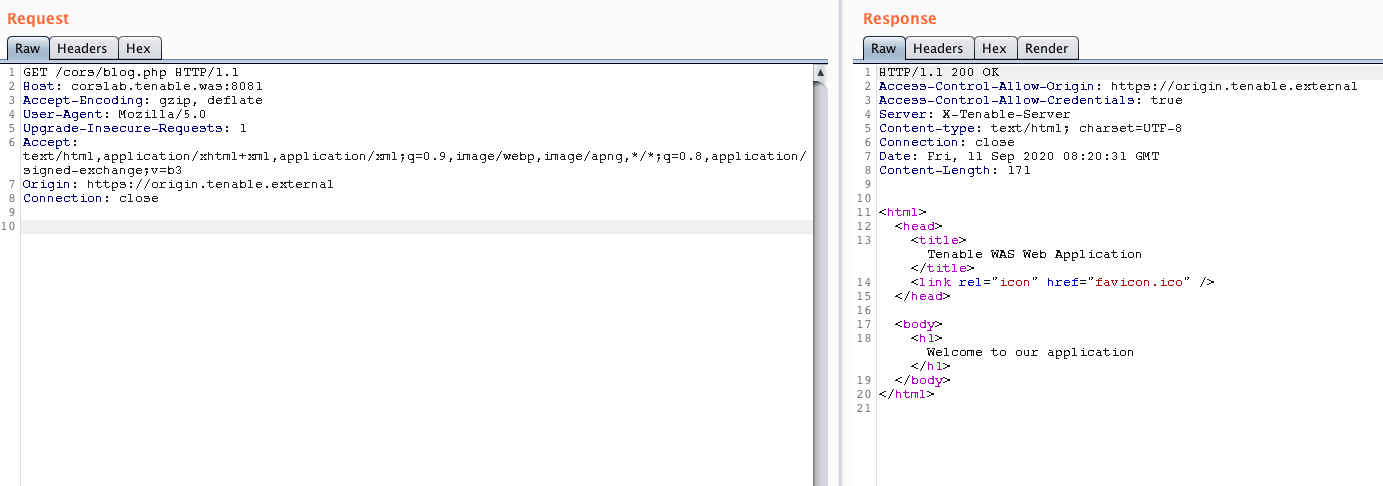
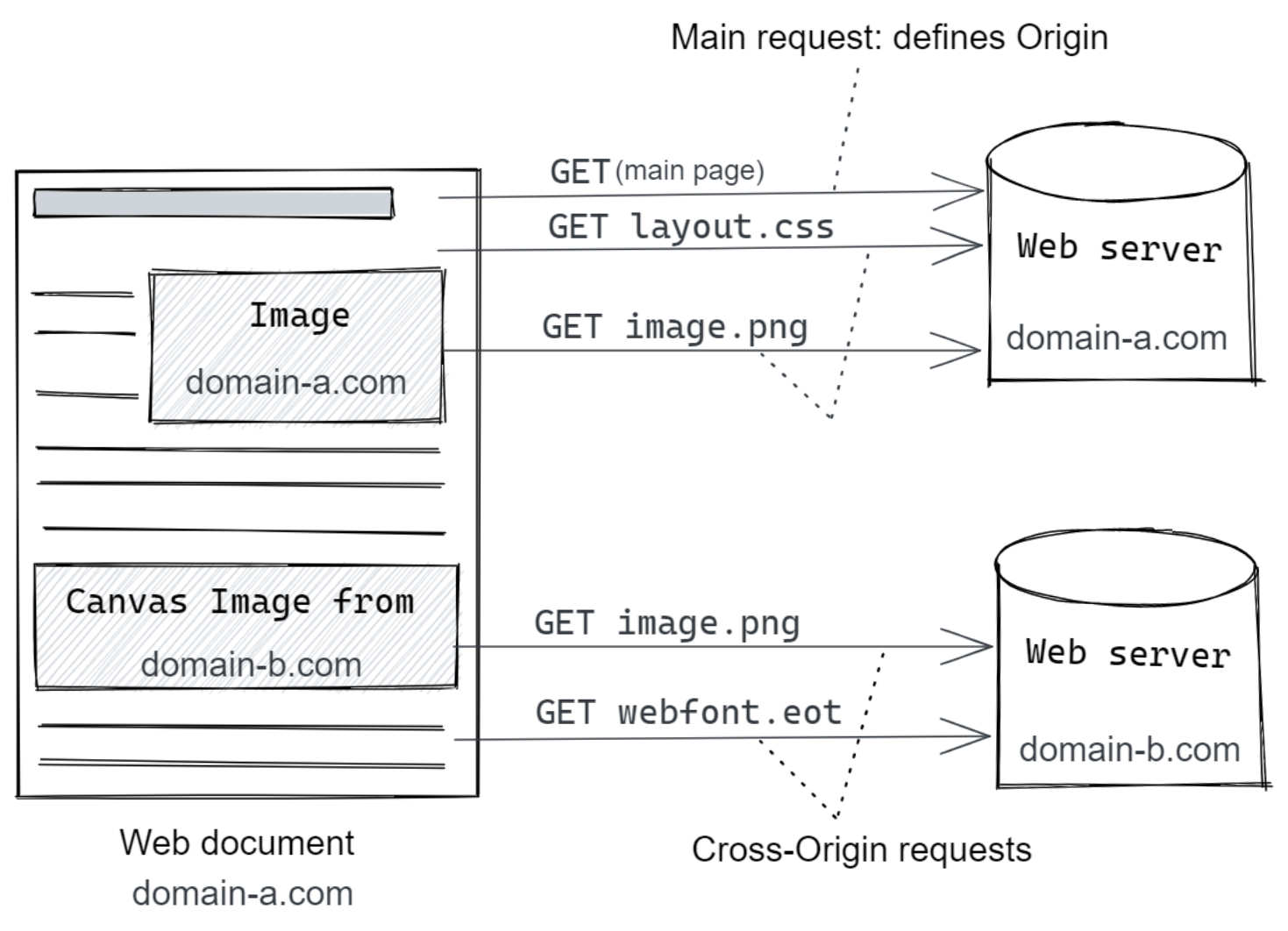
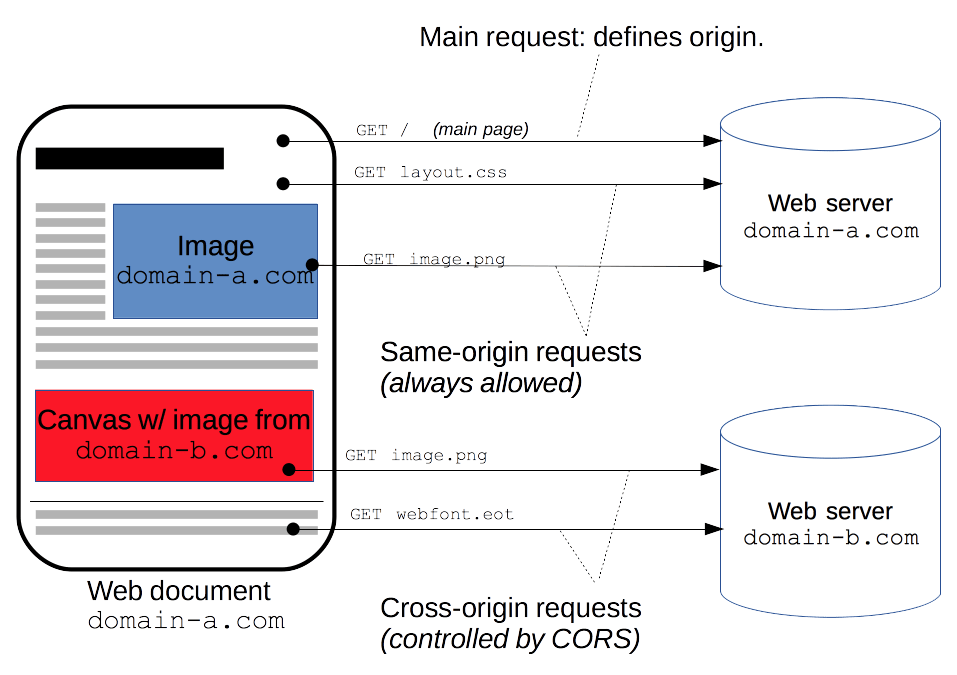
6 Must-Know Things About Cross-Origin Resource Sharing (CORS) | by GP Lee | JavaScript in Plain English
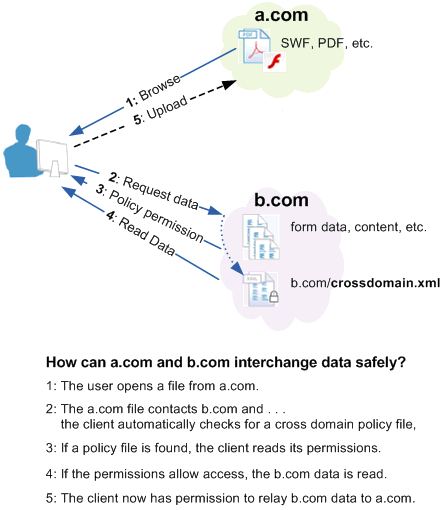
![PDF] An empirical study on the security of cross-domain policies in rich internet applications | Semantic Scholar PDF] An empirical study on the security of cross-domain policies in rich internet applications | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/8b988165c663836cc5de52df21fa7c3b528e269d/5-Figure6-1.png)